Microsoft Secure Future Initiative, Universal Identity Graph, PlainID+ZScaler, Hydden Appears, Crowdstrike+Entra
Microsoft and Secure Future Initiative
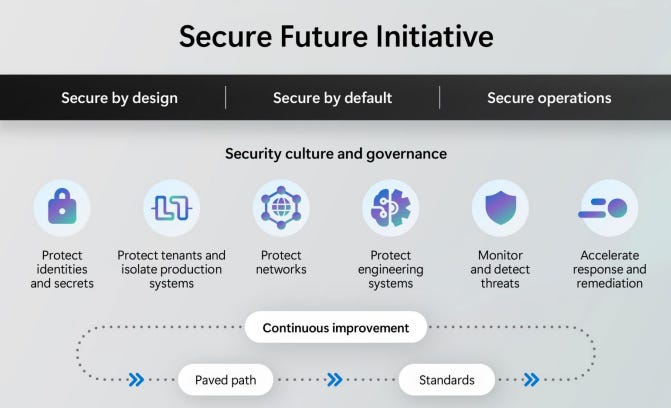
Microsoft have provided an update to something they call their “Secure Future Initiative” - their entire culture and technology approach to secure by design, by default and operationally which they launched in November 2023. They provide regular updates to their progress via insightful reports.
Cultural highlights for September’s report, included “Security as #1 priority: Security added as a core priority for all employees, measured against all performance reviews. Microsoft’s senior leadership team’s compensation is now tied to security performance.” I wonder what number it was at before SFI started?
Specifically from an identity engineering point of view the report stated:
“We completed updates to Microsoft Entra ID and Microsoft Account (MSA) for our public and US government clouds to generate, store, and automatically rotate access token signing keys using the Azure Managed Hardware Security Module (HSM) service. We have continued to drive broad adoption of our standard identity SDKs which provide consistent validation of security tokens. This standardized validation now covers more than 73% of tokens issued by Microsoft Entra ID for Microsoft owned applications.”
Image Source: Microsoft SFI September 2024 Progress Report
From a key learning point of view the report says “Attackers are exploiting user authentication using password spray or phishing as well as token theft and replay techniques, applying these techniques across both user and service accounts to obtain initial footholds in networks.”. Whilst not much of a surprise, it’s good to have these concerns validated by large scale providers.
From a progress point of view the reports adds that access token signing keys have been migrated to be stored within hardware security modules for public and US federal clouds.
A final interesting comment, is the use of video proofing for credential reset flows.
“To enhance our internal employee authentication procedures, we have implemented video-based user verification for 95% of Microsoft internal productivity environment users based on the NIST standards for mid-assurance identity proofing (NIST SP 800-63-4). This solution helps to verify a user’s identity, including remote employees, before granting them access to corporate resources, ensuring credentials are securely transmitted.”
Permiso Launch Universal Identity Graph
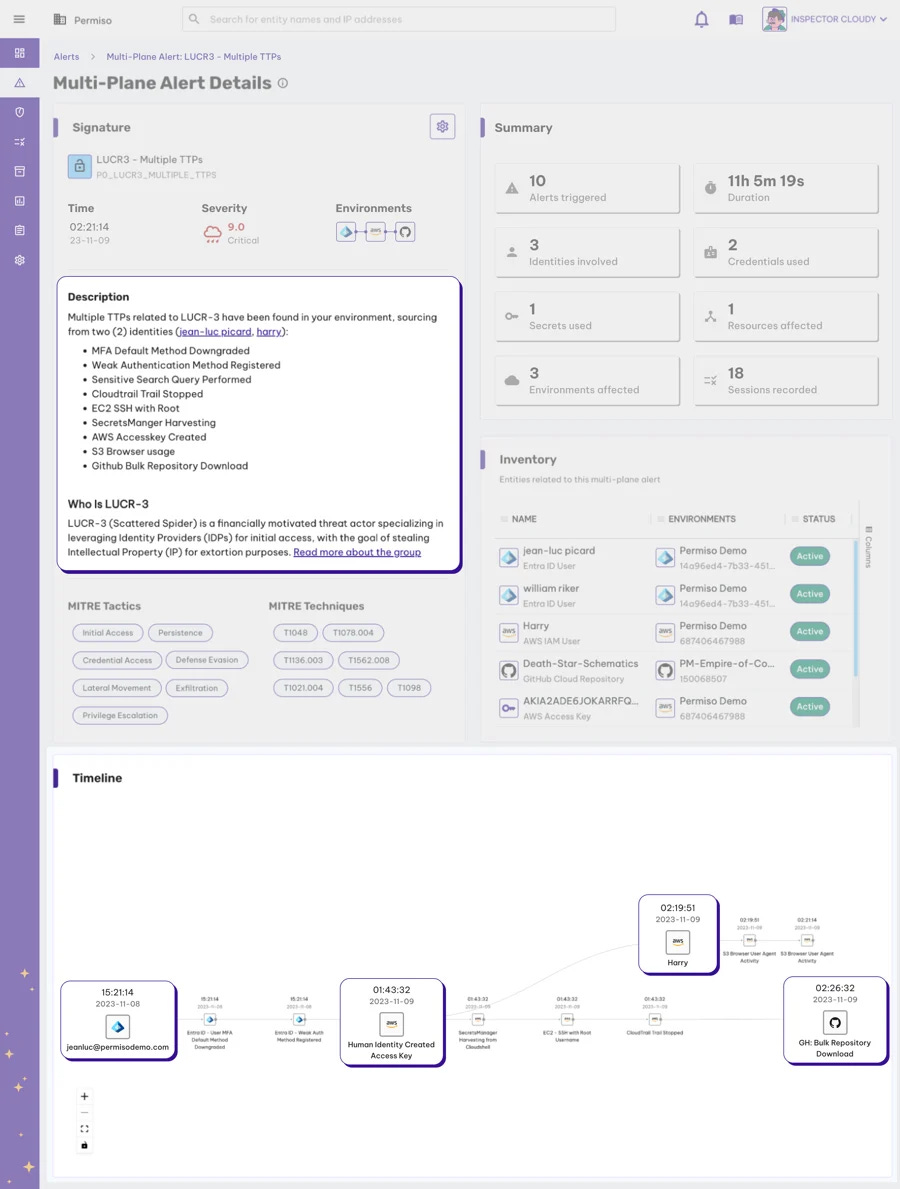
ISPM (identity security posture management) and ITDR (identity threat detection and response) startup Permiso have provided an update on a new capability release they’re calling the Universal Identity Graph.
As organisations struggle with alert fatigue and a myriad of cloud services that has enlarged an already poorly understood identity attack surface, the Universal Identity Graph aims to help solve some of these issues according to Permiso:
“That is why Permiso Security was founded, to comprehensively deal with identity risks and threats across a fragmented ecosystem, with the focus on addressing the greatest threat vector, insecure human, and non-human identities. Through the Universal Identity Graph, Permiso tracks all-entity identities (human and non-human) and their relationships to other identities, credentials, and assets, across multiple environments (IdP -> IaaS -> PaaS -> SaaS).”
The ability to provide end to end link of identity run time and persistent data will be of huge benefit to many organisations with an distributed array of assets.
Image Source: Permiso Blog
A combination of 1000 detection rules and machine machine will allow organisations to reduce external anomalous behaviour as well as more subtle issues with insider threat.
PlainID and Zscaler Mashup
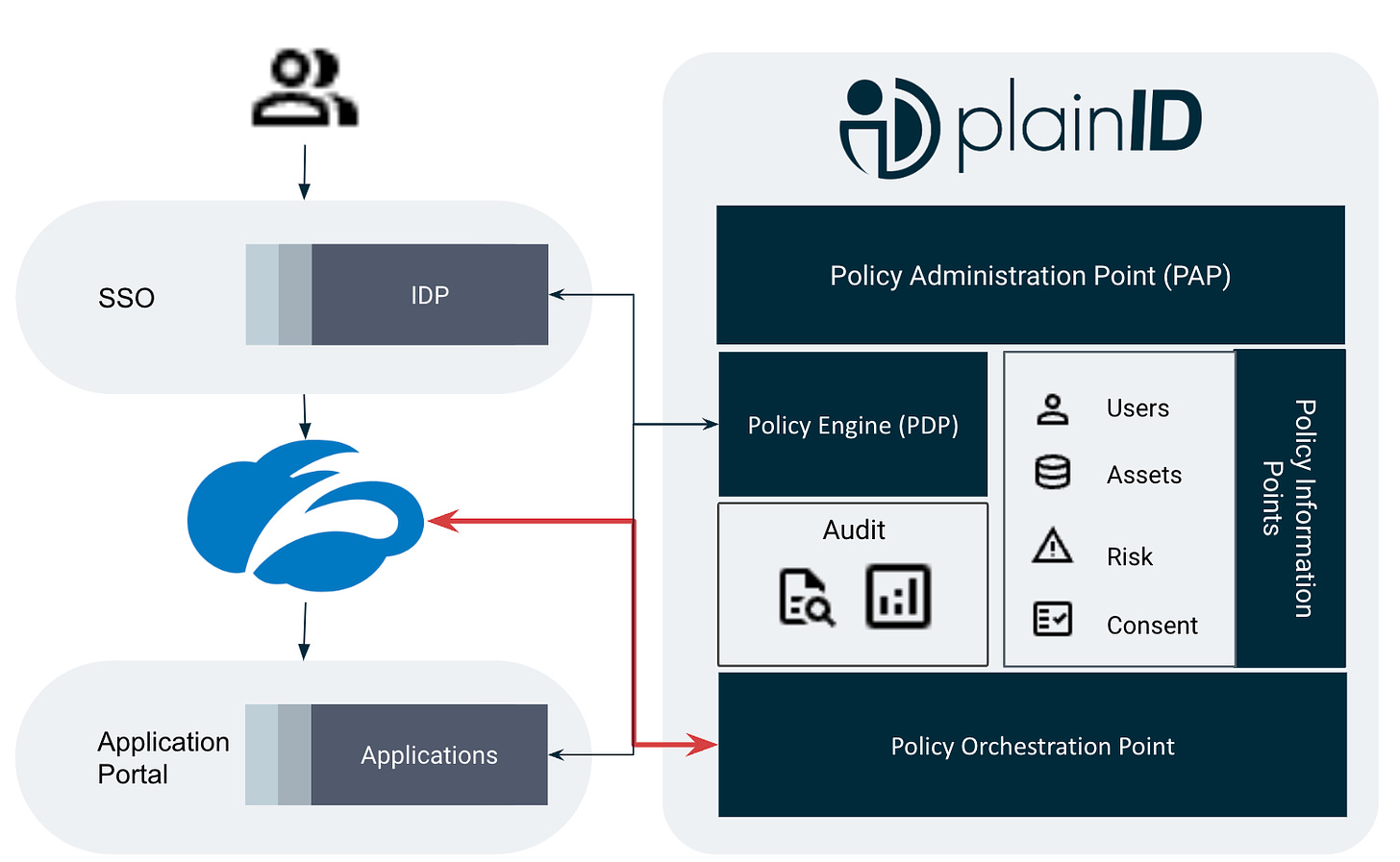
External authorization provider PlainID, have announced an integration with secure access service edge provider ZScaler. The latter’s ZPA (private access) product provides zero trust remote access for internal applications.
“The PlainID Platform supports policy orchestration for Zscaler by allowing PlainID users to discover native Zscaler access control policies and enabling visibility, manageability and editability of the Zscaler policies.”
Image Source: PlainID Integration Hub
Further information is available from the PlainID integration hub.
Hydden Appears with $4.4M Funding
Hydden have appeared out of stealth with the announcement of a $4.4 million funding round.
They describe themselves as the “Identity Visibility Company” where they aim to support business leaders in having visibility across all identities and accounts within the hybrid landscape.
“The platform connects to existing IAM tools, cloud applications, and on-premises systems to build a real-time source of truth about the identity ecosystem. Hydden’s continuous discovery engine detects, classifies, and alerts on identity-related risks so security teams can quickly investigate and respond.”
Visibility is indeed a key part of any end to end IAM risk management process, and typically falls into the NIST Cyber Security Framework’s “identify” bucket. Alas, many organisations struggle in this area - due to legacy technology, isolation and complex integrations.
Hydden aims to:
“Within the volume of data identity tools generate, Hydden finds critical issues that others miss.
Hydden builds a single data layer across identity security solutions, including IAM, PAM, IGA, and ITDR. It cleans, normalizes, correlates, and models data so that any system can act on the information.
Connectors automatically discover and interpret identity data wherever it lives, whether a container in a cloud platform or a mainframe in an on-premise data center.
Continuous discovery surfaces new identity-related issues without compromising resources or impacting operations.
A time capsule of identity history identifies patterns and informs post-event forensics and root cause analysis.”
Crowdstrike Falcon ID and Entra Integration
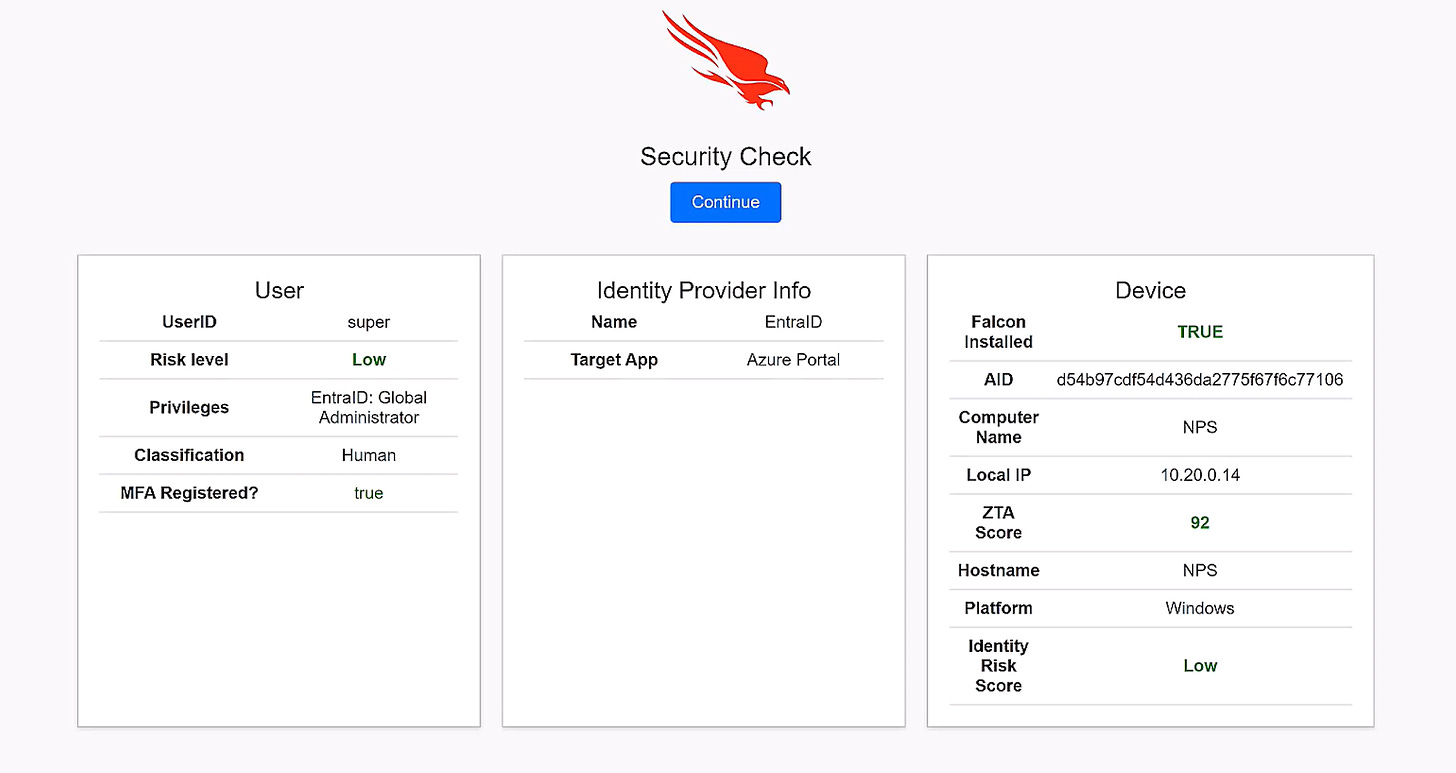
Crowdstrike have announced their Falcon Identity Protection suite is integrated with several aspects of the Microsoft Entra platform.
The release goes on to describe how capabilities such as ITDR, ISPM and PAM (privileged access management) are no longer enough and how Crowdstrike FIP aims to fill any missing gaps.
“As more organizations rely on cloud-based identity providers like Microsoft Entra ID, adversaries are sharpening their focus on these vital systems. Threat actors are deploying increasingly sophisticated tactics, ranging from password spraying to advanced phishing attacks, to exploit misconfigurations and bypass weak multifactor authentication (MFA) processes.”
Image Source: Crowdstrike press release
Crowdstrike are doubling down on the real time aspect with “dynamic access decisions” and “risk based conditional access”. It integrates with Entra via their “External Authentication Method”.